The ACA Group recently sent out an article about detecting phishing emails. We added some comments to the article to help explain more about detecting a phishing email.
Analyzing the email for indications of phishing provides an opportunity to prepare against future similar attempts. The screen capture below of an email sent to ACA has been marked with numbers corresponding to the elements that implicate this email as a phishing attempt.
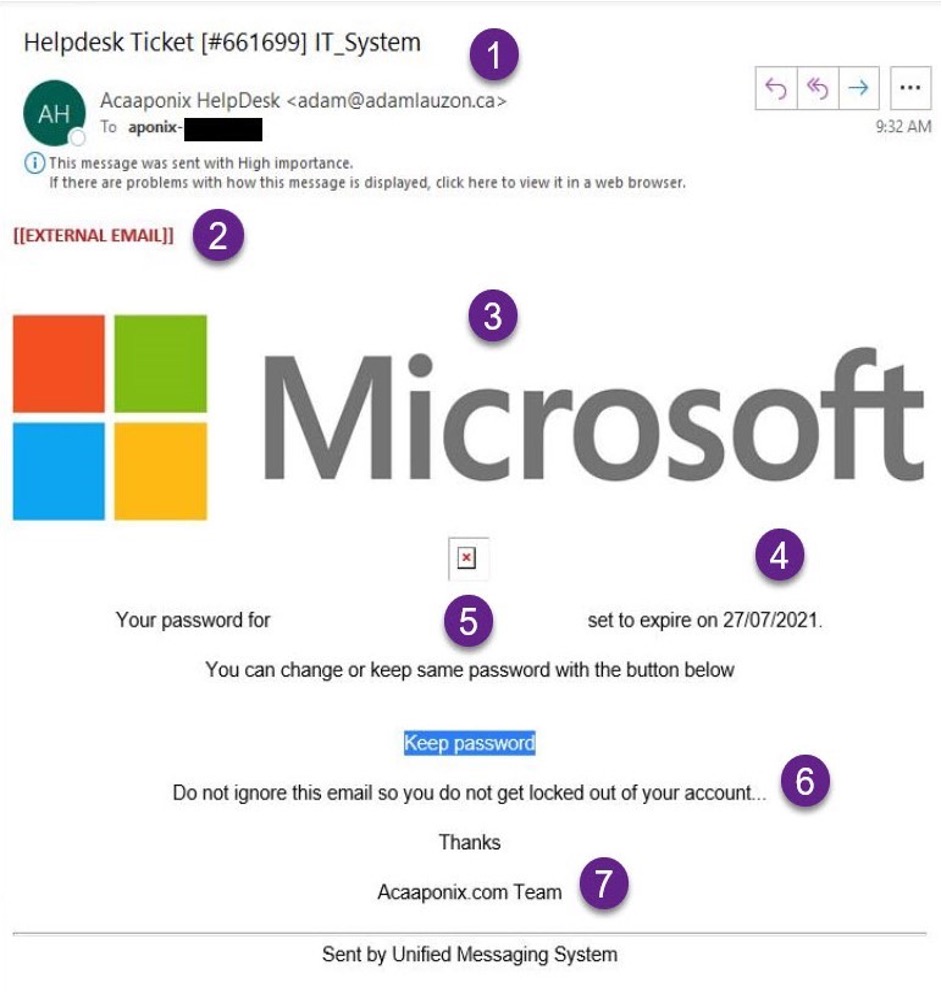
- Sender Address – The email comes from a non-ACA email address, though it purports to be from ACA. Similarly, the address is from a Canadian domain, which is unusual for ACA internal processes.
The email address used, does not go with the name. This is considered spoofing, when someone pretends to be someone or something to gain access to your systems, steel data, steel money or infest your system. - Unsolicited – This email comes from an external source, though it purports to be related to internal ACA processes.
This email was not expected, which is a warning sign it could be a phishing attempt. - Microsoft – The requests purport to come from Microsoft. Statistics indicate that Microsoft is the most spoofed brand by a large margin, comprising 43% of all company impersonations. Hackers use Microsoft logos and websites to make the end user feel safe, because it is made to look like it is from Microsoft.
- Strange Text – The date format is different from the expected U.S. MM/DD/YYYY.
- Bad Spelling/Grammar – The text is missing an article and is awkwardly worded. This is always a warning sign that it is a phishing email.
- Urgent Request – The text calls for urgent action (though no previous warnings have been received, etc.). Scare tactic is used to make the end-user panic and do something without thinking about it first. If the email looks suspicious take your time looking it over. If possible, call the person it came from to confirm it is legit. If from a service you use go to the service website, DO NOT CLICK on the link in the email. When you log into the service website, they will have a note if any issues with their system or your account. If nothing noted, then it was a phishing attempt to try and gather your credentials.
- Email Signature – The signature is not typical for ACA services or groups, or specifically for the Aponix division. “ACA” is not capitalized as well, a further indication of spoofing. This can be hard to detect because hackers can copy email signatures from legit emails.
I know this is not a technical term but listen to your gut. If something does not feel right or does not look legit; then it probably is not. Use the steps above as guidelines to detect a phishing email.
Think Before You Click
David H. Coull
Senior Systems Analyst
210.805.0171